QuantVision
What is a QuantVision?
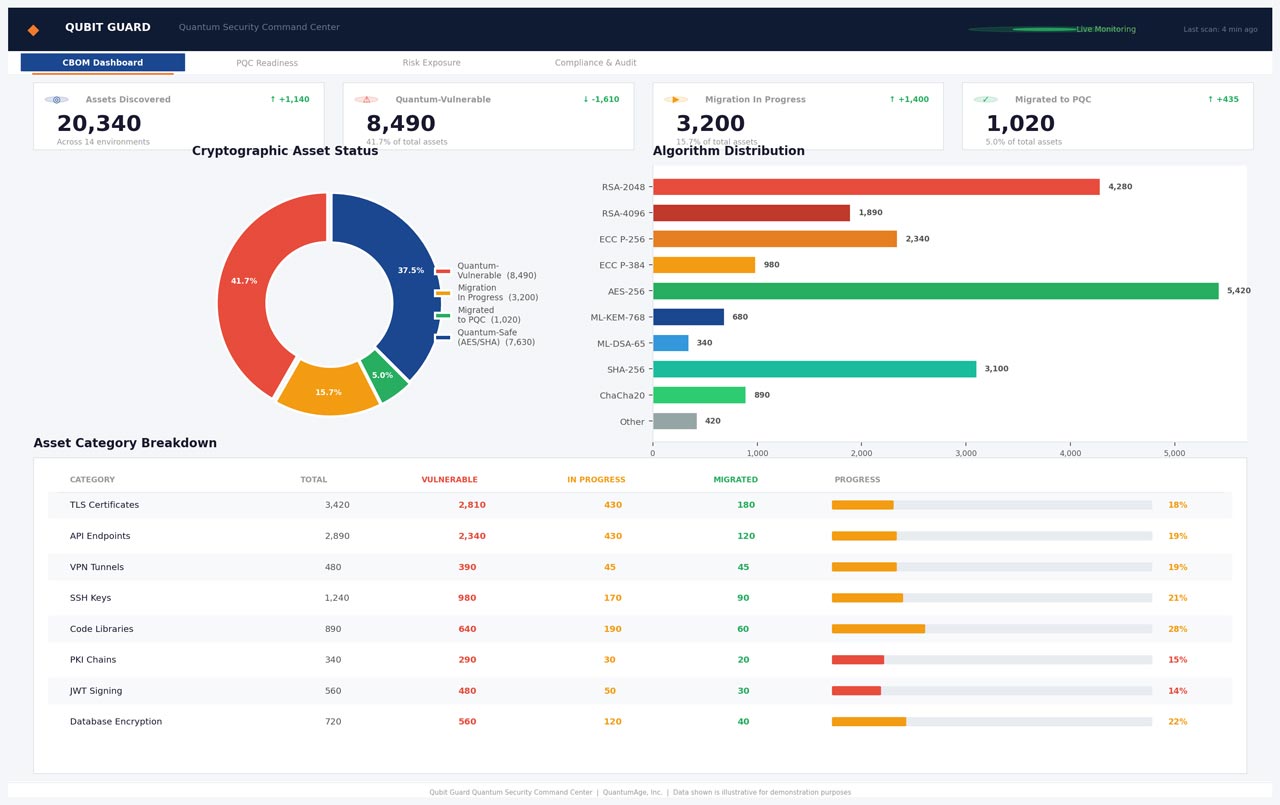
A QuantVision (CBOM) is a complete, continuously updated inventory of all cryptographic assets used across an organization’s applications, infrastructure, networks, and cloud environments.
A QuantVision answers a simple but critical question:
“Where, how, and how well is cryptography being used across our systems?”

A QuantVision typically includes
- Cryptographic algorithms (RSA, ECC, AES, SHA-1/2, ML-KEM, etc.)
- Key sizes and parameters (RSA-2048 vs 4096, AES-128 vs 256)
- Protocols (TLS 1.0–1.3, SSH, IPsec, JWT, OAuth)
- Certificates and PKI artifacts (issuers, expiry, trust chains)
- Cryptographic libraries and dependencies (OpenSSL, BouncyCastle, JSSE, HSMs)
- Where crypto is implemented (apps, APIs, VPNs, load balancers, devices)
You cannot secure, modernize, or migrate cryptography you cannot see.
Why QuantVision Is Critical Now
1. Cryptography Is the New Attack Surface
Most modern breaches do not start with users — they start with:
- Weak or legacy algorithms
- Expired or misconfigured certificates
- Inconsistent crypto implementations across environments
- Hard-coded keys and undocumented dependencies
A single weak cryptographic component can compromise entire systems.
2. Quantum Risk Makes “Hidden Crypto” Dangerous
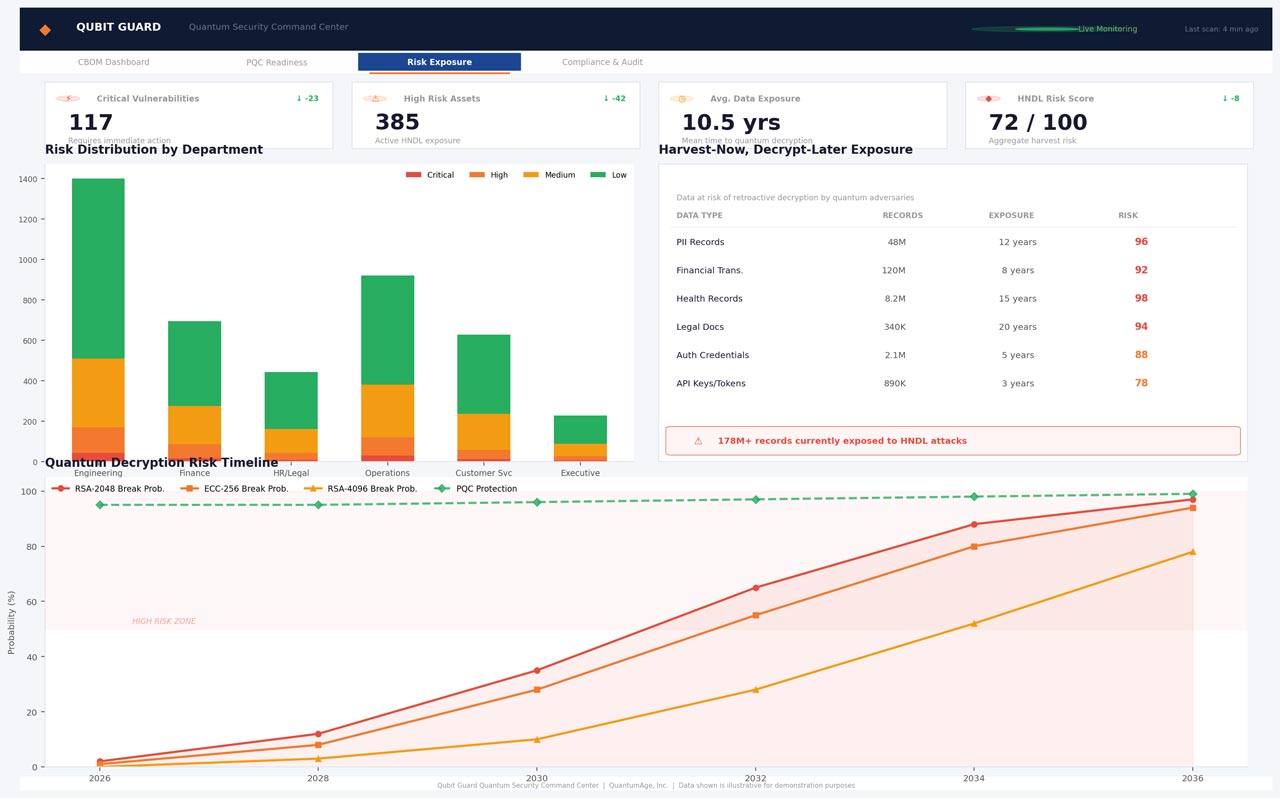
Post-quantum threats introduce a new class of risk:
- Harvest Now, Decrypt Later (HNDL)attacks
- Long-lived data (PII, financial records, health data, classified data) is already being collected for future decryption
- RSA and ECC are mathematically vulnerable to quantum algorithms like Shor’s algorithm
Without a QuantVision, organizations do not know:
- Which systems are quantum-vulnerable
- Which data is already at long-term risk
- Where to begin PQC migration
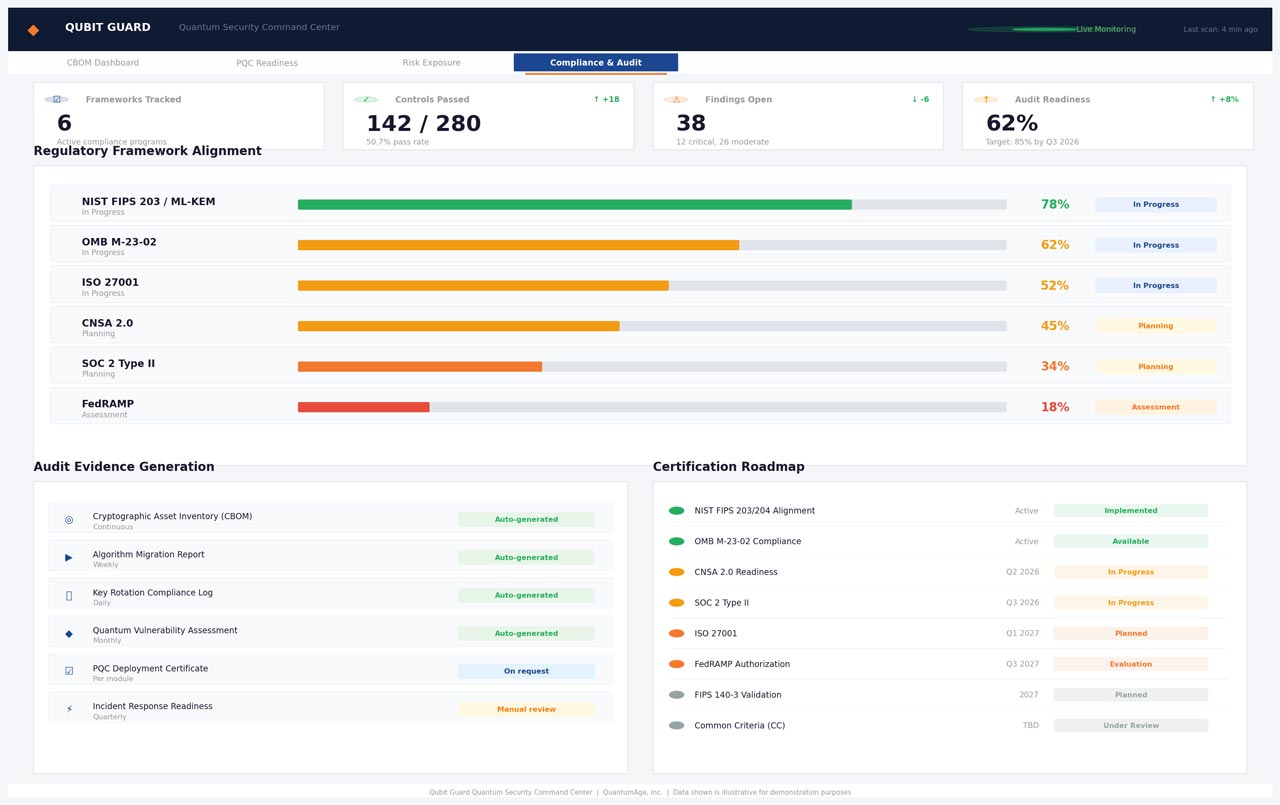
3. Regulations Are Moving Faster Than Most Organizations
Governments and regulators increasingly expect:
- Documented cryptographic inventories
- Evidence of crypto agility
- Defined migration plans toward post-quantum cryptography
QuantVision is rapidly becoming the cryptographic equivalent of SBOM — not optional, but expected.

Why Enterprises Need Regular Cryptographic Audits
- Identify weak, deprecated, or non-compliant algorithms
- Prevent silent cryptographic failures before breaches occur
- Avoid outages caused by expired certificates
- Reduce firefighting during TLS, PKI, or platform upgrades
- Safely modernize APIs, cloud workloads, and zero-trust architectures
- Enable controlled migration to hybrid and post-quantum cryptography
- Instantly understand crypto blast radius during a vulnerability disclosure (e.g., OpenSSL-type events)
Why Government Agencies Need CBOM
For government and public sector organizations, CBOM is foundational to:
National & Public Safety
- Protect sensitive, long-lived data from future quantum decryption
- Reduce systemic risk across interconnected agencies and vendors
Compliance & Audit Readiness
- Demonstrate cryptographic governance to oversight bodies
- Support federal and state cybersecurity mandates
Vendor & Supply-Chain Risk Management
- Validate cryptographic posture of third-party systems
- Reduce dependency on undocumented or insecure vendor crypto
Mission Continuity
- Prevent cryptography-related outages in critical services
- Enable planned, phased modernization instead of emergency upgrades
Why Cryptographic Audits Must Be Regular (Not One-Time)
Cryptographic posture changes constantly due to:
- Software updates and new deployments
- Certificate renewals and expirations
- New cloud services and APIs
- Emerging vulnerabilities and regulatory changes
- Advancements in classical and quantum computing
A one-time crypto assessment becomes obsolete quickly.
Best practice:
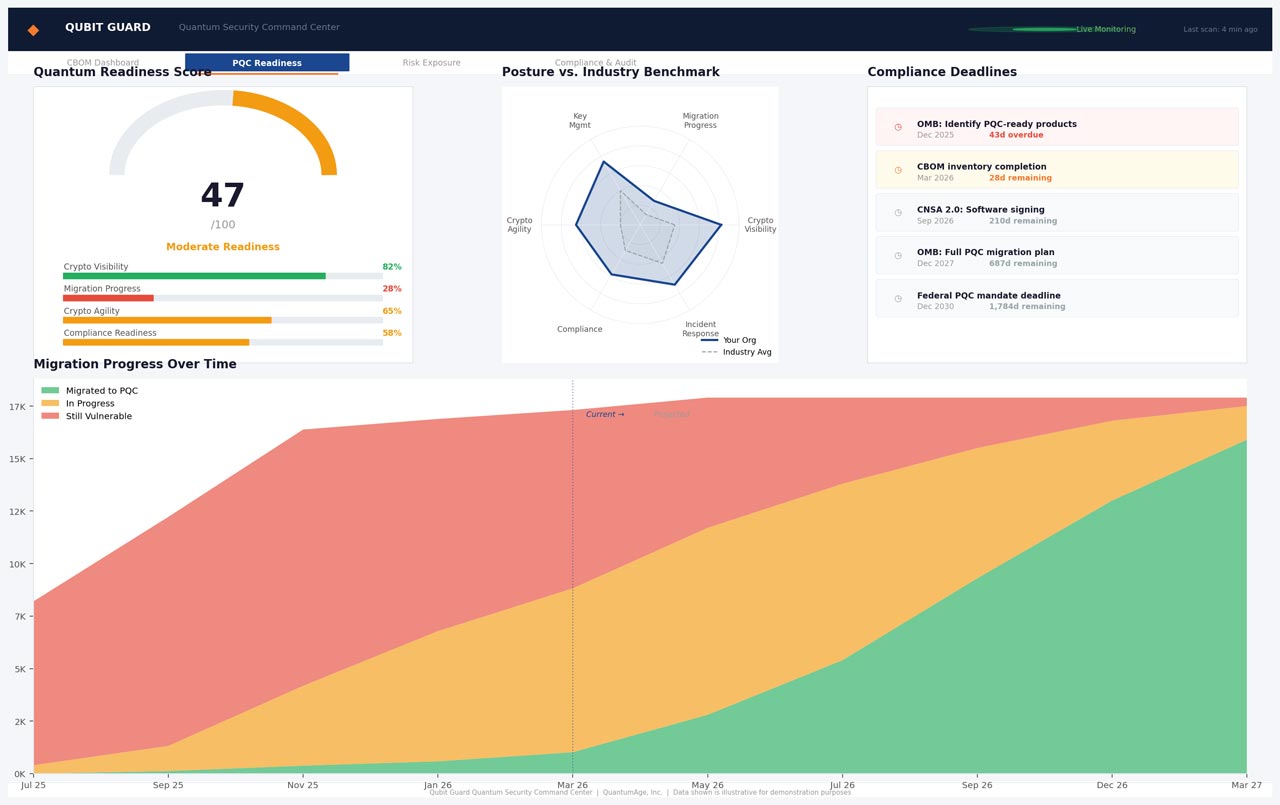
- Continuous or periodic QuantVision scans
- Risk scoring and trend tracking over time
- Audit-ready reporting for security, compliance, and leadership teams

QuantVision as the Foundation for Quantum-Safe Security
QuantVision is not just an inventory — it is the starting point for:
- Crypto agility
- Post-quantum migration planning
- Zero-trust and secure-by-design architectures
No organization can credibly claim “quantum readiness” without a QuantVision.
FAQs
Frequently Asked Questions
The Short Answer: It is a CBOM (Cryptographic Bill of Materials) dashboard.
The Enthusiast Answer: Think of it as an “X-ray” for your software’s security. While standard scanners look for surface-level bugs, QuantVision looks at the math (the cryptography) holding your house together. It identifies every lock, key, and signature to ensure they aren’t “Quantum-Vulnerable.”
SHA-256 is just a digital fingerprint—it tells you if the data changed. HMAC-SHA256 adds a Secret Key to that fingerprint.
- SHA-256 is like a seal on a letter.
- HMAC-SHA256 is like a seal that only glows under a specific UV light that only you and the recipient own. It proves the data is both intact and authentic.
A JWT (JSON Web Token) is like a Digital VIP Wristband.
- Stateless means the server doesn’t need to “remember” who you are.
- Instead of looking you up in a database every time you click a button, the server just checks the HMAC-SHA256 signature on your wristband. If the signature is valid, you’re in. This allows apps to scale to millions of users without slowing down.
These are the new CNSA 2.0 standards designed to survive a quantum computer attack:
- ML-KEM (The Vault Builder): Used for safely sending secret keys. (Replaces RSA/Diffie-Hellman).
- ML-DSA (The Notary): Used for digital signatures to prove who you are. (Replaces RSA-Sig/ECDSA).
These are Stateful Hash-Based Signatures. They are used for ultra-critical things like Firmware Updates. Unlike other math that might be “guessed” one day, these use a mathematical “tree” where every signature is carved in stone. They are incredibly secure but require perfect “bookkeeping” (you can’t use the same “leaf” twice).
- Hardcoded: Welding a specific lock onto a door. If the lock breaks, you have to tear the wall down to fix it.
- Direct Call: Ordering a specific brand of lock by name. If that brand goes bankrupt (or the algorithm is hacked), your code won’t work.
- The Fix: We use the Factory Pattern, which allows the app to just ask for a “High-Security Lock” and lets the system pick the best one available that day.
It’s the “Wild West.” It’s when every developer in your company picks their own encryption methods and hides their own keys. QuantVisionfixes this by creating a Centralized Map (the CBOM) so you can manage your security from one cockpit.
It’s a 0–10 “Danger Thermometer”:
- 9.0 – 10.0 (Critical): The house is on fire. Fix it now.
- 7.0 – 8.9 (High): A hacker is at the door. Fix it this week.
- 4.0 – 6.9 (Medium): There’s a crack in the window. Fix it soon.
- CWE (The Weakness): The “Bad Habit.” (e.g., “Leaving the door unlocked.”)
- CVE (The Vulnerability): The “Specific Event.” (e.g., “The back door of Office Building A was found unlocked on Tuesday.”)
QuantVision tracks both to help you fix the specific bug and train your team to stop making the mistake.
It’s the ultimate goal. It means your software is designed so you can swap out encryption algorithms instantly without rewriting any code. It’s the difference between a hard-wired lamp and one you can just unplug and move to a new outlet.
Key Takeaway
QuantVision transforms cryptography from a hidden technical detail into a governed, measurable, and future-proof security control.
For enterprises, it reduces risk and operational chaos.
For governments, it protects long-term data, public trust, and national interests.
FAQs
QubitVision Frequently Asked Questions
The Short Answer: It is a CBOM (Cryptographic Bill of Materials) dashboard.
The Enthusiast Answer: Think of it as an “X-ray” for your software’s security. While standard scanners look for surface-level bugs, QuantVision looks at the math (the cryptography) holding your house together. It identifies every lock, key, and signature to ensure they aren’t “Quantum-Vulnerable.”
SHA-256 is just a digital fingerprint—it tells you if the data changed. HMAC-SHA256 adds a Secret Key to that fingerprint.
- SHA-256 is like a seal on a letter.
- HMAC-SHA256 is like a seal that only glows under a specific UV light that only you and the recipient own. It proves the data is both intact and authentic.
A JWT (JSON Web Token) is like a Digital VIP Wristband.
- Stateless means the server doesn’t need to “remember” who you are.
- Instead of looking you up in a database every time you click a button, the server just checks the HMAC-SHA256 signature on your wristband. If the signature is valid, you’re in. This allows apps to scale to millions of users without slowing down.
These are the new CNSA 2.0 standards designed to survive a quantum computer attack:
- ML-KEM (The Vault Builder): Used for safely sending secret keys. (Replaces RSA/Diffie-Hellman).
- ML-DSA (The Notary): Used for digital signatures to prove who you are. (Replaces RSA-Sig/ECDSA).
These are Stateful Hash-Based Signatures. They are used for ultra-critical things like Firmware Updates. Unlike other math that might be “guessed” one day, these use a mathematical “tree” where every signature is carved in stone. They are incredibly secure but require perfect “bookkeeping” (you can’t use the same “leaf” twice).
- Hardcoded: Welding a specific lock onto a door. If the lock breaks, you have to tear the wall down to fix it.
- Direct Call: Ordering a specific brand of lock by name. If that brand goes bankrupt (or the algorithm is hacked), your code won’t work.
- The Fix: We use the Factory Pattern, which allows the app to just ask for a “High-Security Lock” and lets the system pick the best one available that day.
It’s the “Wild West.” It’s when every developer in your company picks their own encryption methods and hides their own keys. QuantVisionfixes this by creating a Centralized Map (the CBOM) so you can manage your security from one cockpit.
It’s a 0–10 “Danger Thermometer”:
- 9.0 – 10.0 (Critical): The house is on fire. Fix it now.
- 7.0 – 8.9 (High): A hacker is at the door. Fix it this week.
- 4.0 – 6.9 (Medium): There’s a crack in the window. Fix it soon.
- CWE (The Weakness): The “Bad Habit.” (e.g., “Leaving the door unlocked.”)
- CVE (The Vulnerability): The “Specific Event.” (e.g., “The back door of Office Building A was found unlocked on Tuesday.”)
QuantVision tracks both to help you fix the specific bug and train your team to stop making the mistake.
It’s the ultimate goal. It means your software is designed so you can swap out encryption algorithms instantly without rewriting any code. It’s the difference between a hard-wired lamp and one you can just unplug and move to a new outlet.

